

I’ve questions about this.
People are talking about it like it is the greatest thing ever, however, isn’t this yet another result of the Broadcom acquisition? After firing a bunch of people , now this. Maybe they just don’t want to maintain the “existing proprietary virtualization code” so they’re moving to KVM. Less costs, less people.











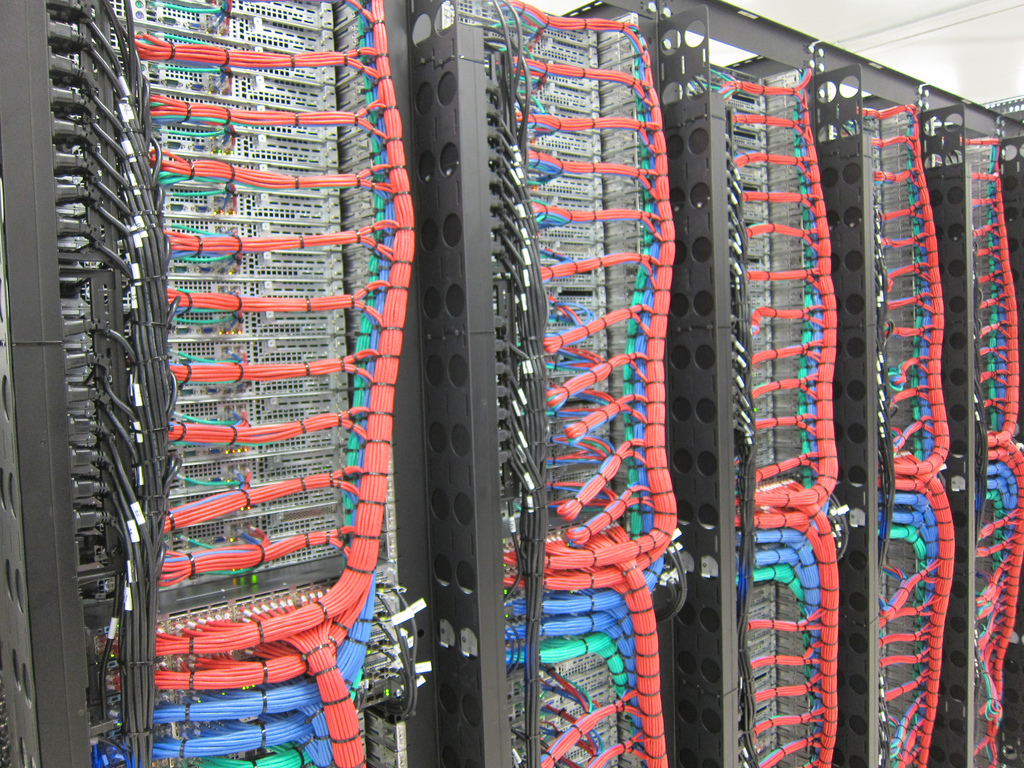




Yeah but VMware was good. And I’m not seeing Broadcom investing into porting the “proprietary goodness” of VMware into KVM. I just see then looking at KVM and saying “that’s good enough” and seeing it a cost reduction measure.